Unlocking the Code: Understanding Gaming Security Encryption
In the digital realm of gaming, security encryption plays a pivotal role in safeguarding user data and maintaining the integrity of gameplay. As online gaming continues to expand, developers have recognized the necessity of implementing robust encryption protocols to protect against data breaches and cyber threats. By encrypting sensitive information such as player credentials, in-game transactions, and personal details, developers can significantly reduce the risk of unauthorized access, ensuring a safer environment for gamers.
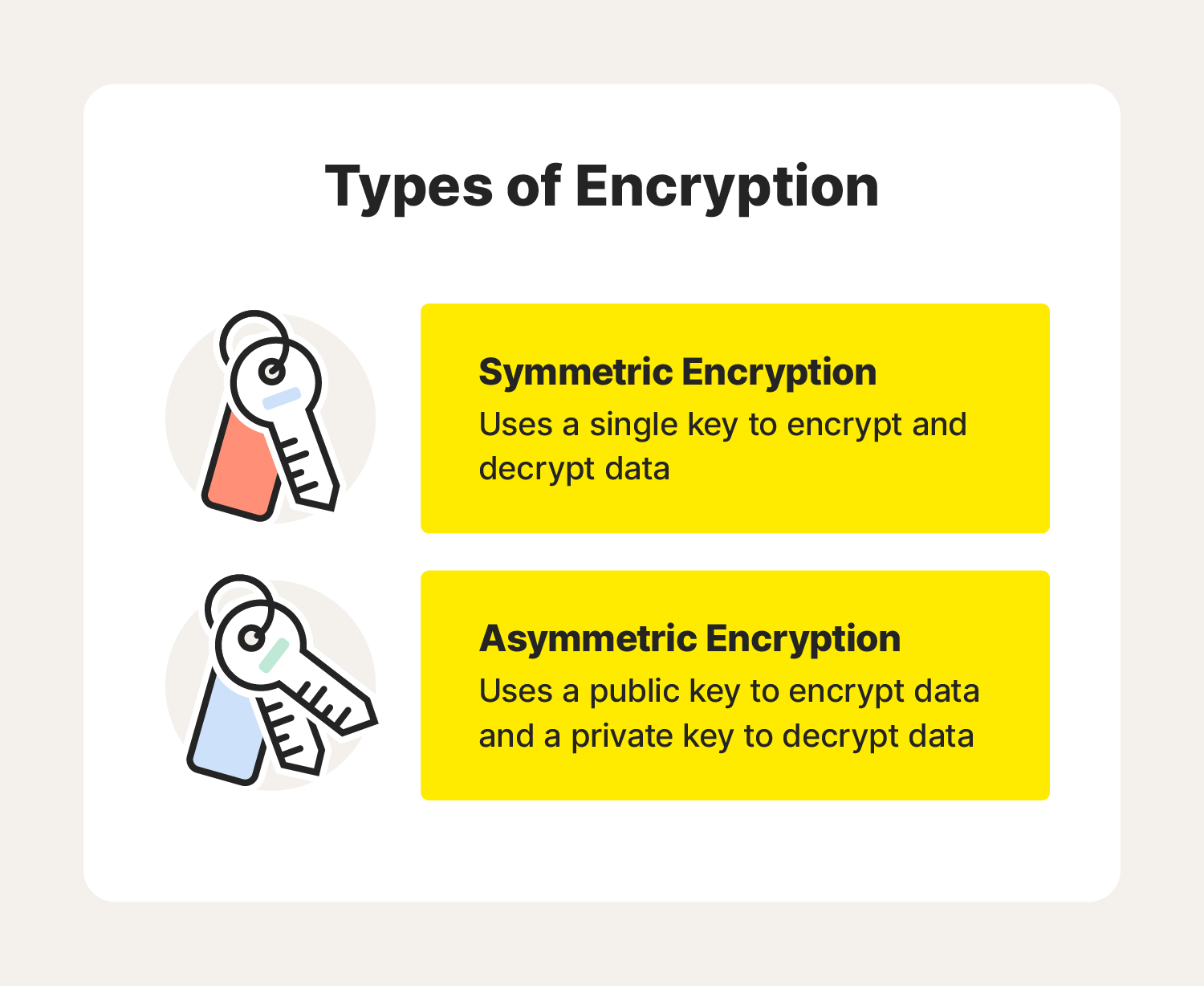
Understanding how gaming security encryption works involves delving into various methods and technologies, such as SSL/TLS protocols, which establish secure connections between players and game servers. Additionally, symmetric and asymmetric encryption techniques are commonly employed to encrypt data both at rest and in transit. These approaches not only help prevent cheating and hacking but also enhance the overall gaming experience by fostering trust among players. As the gaming industry continues to evolve, the emphasis on strong security measures will remain paramount to protect both developers and players alike.
Counter-Strike is a fast-paced first-person shooter that has captivated gamers since its initial release. Players choose to fight as either terrorists or counter-terrorists in various game modes. For those looking to enhance their gaming experience, using a stake promo code can provide exciting benefits.
Is Your Virtual World Secure? The Importance of Encryption in Gaming
In today's digital age, encryption plays a pivotal role in safeguarding our virtual experiences, especially in the realm of gaming. As online gaming continues to grow in popularity, so does the need for robust security measures. Gamers often share personal information and financial data while engaging with others across global platforms, making them prime targets for cybercriminals. Ensuring that your virtual world is secure involves understanding how encryption works and its significance in protecting sensitive information from potential threats.
Encryption acts as a shield, converting your data into a coded format that can only be read by those who possess the correct decryption key. This makes it nearly impossible for unauthorized users to intercept and exploit your information. In addition, many gaming companies now implement strong encryption protocols to maintain the integrity of online transactions, player accounts, and communications, further enhancing user trust. By prioritizing encryption, both gamers and developers contribute to a safer and more secure gaming environment for all.
Top 5 Encryption Techniques Every Gamer Should Know to Protect Their Data
In the digital age, ensuring the security of your gaming data is paramount, especially with the rise of online gaming and the threats that come with it. Here are the Top 5 Encryption Techniques every gamer should know to protect their data:
- Symmetric Encryption: This method uses a single key for both encryption and decryption, making it fast and efficient for real-time gaming data.
- Asymmetric Encryption: Utilizing a pair of keys (public and private), this technique provides enhanced security for transactions and communications.
- Hashing: Although not traditional encryption, hashing algorithms like SHA-256 can securely verify data integrity, ensuring that your gaming data has not been tampered with.
- End-to-End Encryption: This ensures that data sent between you and the game server is encrypted, providing protection from prying eyes.
- VPN Encryption: Using a VPN can add an extra layer of encryption, shielding your online activity from hackers.
By understanding and implementing these techniques, you can significantly increase your data security while enjoying the gaming experience.